What Is Dkim Authentication?
DKIM authentication is a method used to verify the message sender identity in a mail transfer. This authentication method makes sure that the mail was not tampered with or forged during transit. Read more here
#1
Access unlimited mailboxes from one place
#2
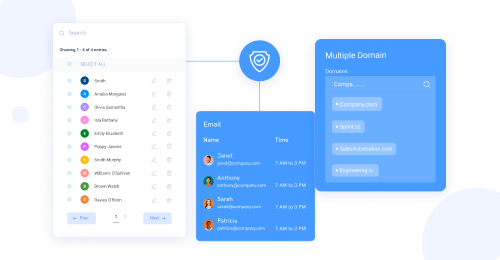
Build brand identity and credibility with unlimited custom domains
#3
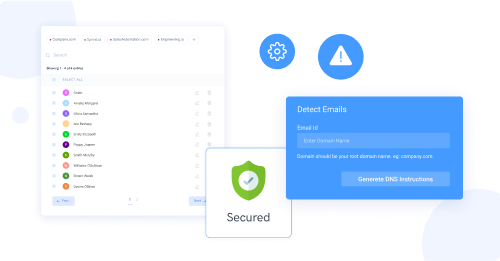
Filter emails to avoid spams for a secured email communication
#4
Export contacts to CRM directly from your address book via CRM integrations
#5
Route emails to various groups using advanced filters and aliases
#6
Set up mailboxes with default email clients without having to download a new one
#7
Enable thread view to simplify mail tracking
#8
Personalize emails with mutiple signatures
#9
Unbelievable pricing - the lowest you will ever find
#10
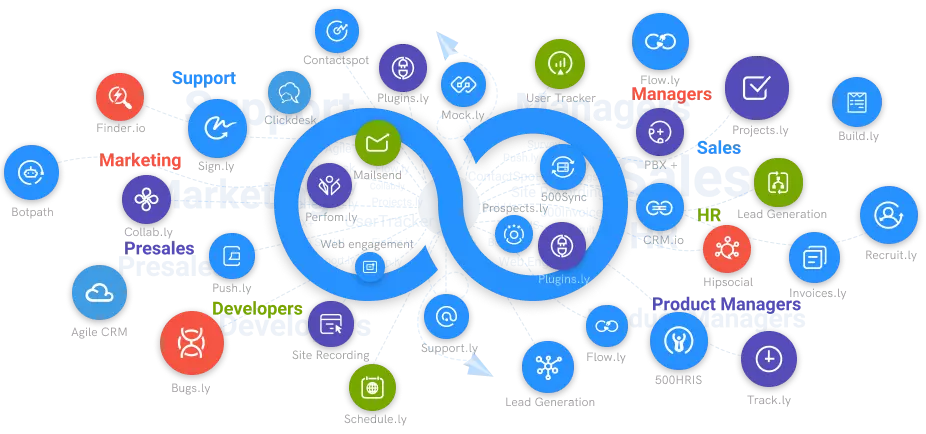
Everything your business needs - 50 apps, 24/5 support and 99.95% uptime
DKIM, an acronym for Domain Keys Identified Mail, refers to a system that prevents spam messages, hacking, and scamming for people that send and receive emails. This tool allows email receivers to verify that a mail received was indeed sent by the domain owner. This is achieved by introducing an electronic signature secured with encryption that confirms its authorization by the sender. This technique also employs security measures that ensure that what is being sent is the same as what is received; in order words, there is no alteration of messages between sending and receiving.
It's important to note that electronic signatures are only validated on the server level; end-users have no access to these signatures. DKIM combines two separate specifications, such as Domain Keys (DK) and Identified Mail (IM). This collaboration evolved into what is now a widely used method of email authentication.
DKIM uses a public key encryption method to sign emails using a private key when they leave the sending server. The receiver's server then verifies the email's source using a public key disclosed to a Domain Name System (DNS). This procedure also ensures that the message's content is not tampered with. Once all these processes are followed and the signature verified, the message is authentic.
Why Is Dkim Authentication Relevant
Having a DKIM authentication for your emails is not compulsory, but it has numerous benefits. When your emails are signed, they come across as more authentic to your receivers, and more often than not, they evade ending up in the spam or junk folder. People who engage in internet fraud are more likely to use domains with a good reputation or a well-known brand. Leaving your domain without DKIM authentication allows these fraudsters to use your domain name and drag your reputation down the mud.
Several layers of security can be established for your sender domain email as DKIM is compatible with other email authentication techniques such as Sender Policy Framework (SPF), Domain-based Message Authentication, Reporting, and Conformance (DMARC).
Additionally, DKIM is used by Internet Service Providers (ISP) to accumulate your record of performance credibility (high engagement, low spam, and bounces) over some time on your domain, which enhances your capacity to deliver.
Our Guide to Set Up Dkim Authentication
Three steps will be discussed as the necessary processes for setting up DKIM authentication.
STEP 1: Generating key pair by configuring the DKIM. This stage is called """"setting up."""" for this process, it is important to note that the choice of tool depends on the operating system of the device used.
STEP 2: In the Domain Name System (DNS) settings, the public key should be placed as a TXT record.
STEP 3: Saving signature after generating it. Sendmail has made this milter open source, and it allows you to sign message headers with a DKIM key that you generate yourself. You can use the DKIM milter when using Sendmail or Postfix or any other Simple Mail Transfer Protocol (SMTP) webserver that endorses the milter.
500Mail.com
**Listed below are some features of 500mail.com in DKIM authentication:
Grants securely access to your email.
Encrypt emails, use physical security, and data security regulations to provide secure Email access for businesses and individuals.
Ensures high-level security while preventing third-party access. In addition, it offers ad-free and privacy-protected services.
Physical Protection: Protect your software, hardware, network, and sensitive information from direct attacks that could harm your business. 500mails protects users from both physical and cyber-attacks.
Email Data Protection offers an email route that is functional on-site or in the cloud to help you improve your cyber security.
End-to-end cryptographic messages are secure throughout the delivery and cannot be made accessible by email web servers.
Secure Email Access Receive a secure email at your end. Your calendar, emails, and contact information are always encoded, and only authenticated users will access them.
- Certificates and Regulatory requirements To protect Email using authentication, you must follow all of the guidelines and criteria. In addition, SSL certification will be provided for encoding email lines of communication.
"